Ravigopal Kesari, a software engineer
who makes
crafts websites & applications.

Interested in leading engineering teams, building systems, improving aesthetics and scaling products.
Notes
I’ve started writing again occasionally when the mood strikes.
You can see all notes, or here are the last couple batches of words:
Deploying Bun application to Fly.io
Steps for deploying application built with Bun
HTML can do that?
Collection of things HTML can do natively
Side projects
A place where I tend to experiment with new frameworks/technologies.
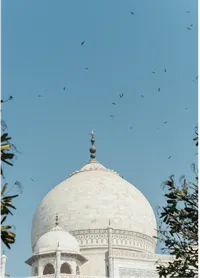
Photography
Try to learn new techniques everyday and getting comfortable with the intricacies of this process of capturing light.